HOW TO
Configure ArcGIS Monitor system counters in AWS
Summary
For monitoring of system counters in Amazon Web Services cloud (AWS), Esri recommends using the Amazon counter type instead of the system counter type and enable monitoring on all instances. All instances can be tracked with the data provided by Amazon CloudWatch. Using this method, the security access is handled through Amazon. If you are unable to follow the above recommendation, and still want to configure a system counter to monitor a hostname in AWS, additional configuration steps described in this article are needed to allow traffic between instances in the security zone.
In this article, we assume that ArcGIS Monitor in the AWS cloud is already installed on a dedicated instance alongside the target deployment you want to monitor before performing these steps.
Procedure
ArcGIS Monitor and target deployment within the same security zone
It is likely that there is a security zone defined around the target deployment. If the ArcGIS Monitor Administrator is within in that security zone, communication is likely allowed between instances.
- Use Windows Perfmon on the ArcGIS Monitor Administrator machine to verify that you can connect to the target hostname in AWS.
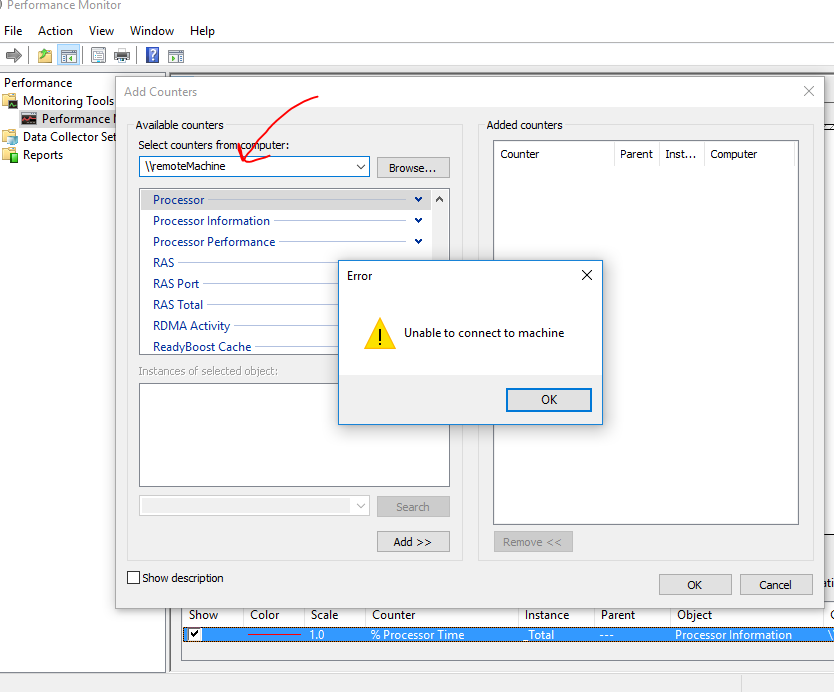
- If the connection is successful, continue to Step 3. If unable to connect, go to the Configure Firewall section below.
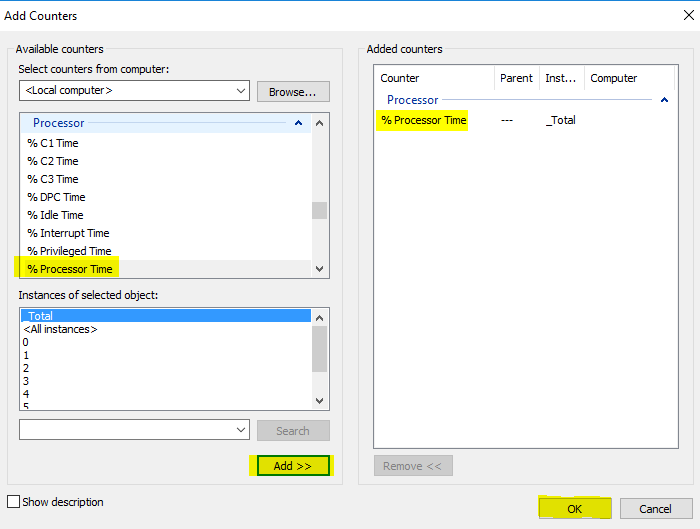
- Add the % Processor Time counter and click OK.
- If it worked, proceed to Add a System counter. No further steps are necessary.
- If it failed to add % Processor Time, check it the Windows user is an Administrator on the target machine. If the Windows user is not an administrator, Configure WMI permissions. After permissions are granted, try Step 3 again.
Configure Firewall
The security zone must be configured to allow traffic between instances in the security zone. We assume that Windows firewall is installed and enabled on each instance.
Access to WMI through the Windows Firewall must be enabled to allow ArcGIS Monitor Administrator to connect to the target instances. Since the security zone provides a shielded boundary around the cloud deployment, both outbound and inbound rules from the instance hosting ArcGIS Monitor Administrator must be considered.
Required are the Group Policy Management Tools on Windows 7, Windows 8, Windows 10, Windows Server 2008, 2012, and 2016. These are part of the Remote Server Administration Tools (RSAT) available from the Microsoft web site.
Instructions
To enable access to WMI on computers using the Windows Firewall with Advanced Security (Windows 7, Windows 8, Windows 10, Windows Server 2008, 2012, and 2016) please follow these steps.
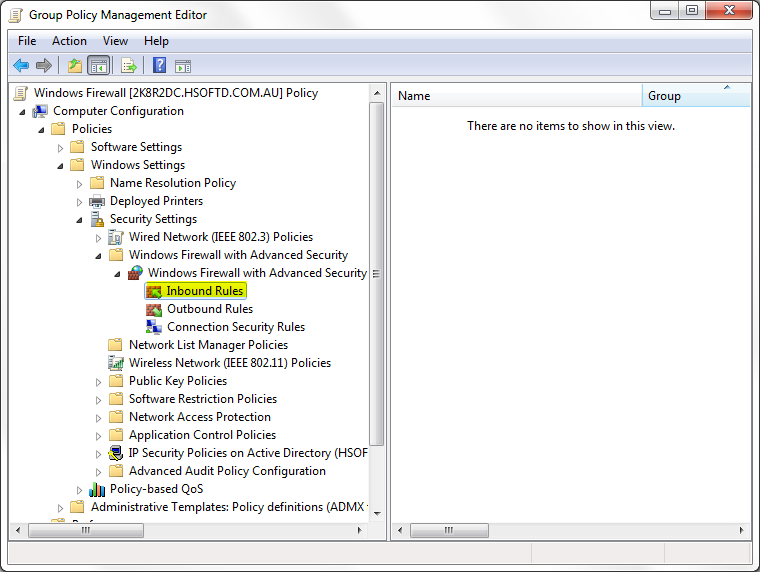
- Edit an existing Group Policy object or create a new one using the Group Policy Management Tool.
- Expand Computer Configuration > Policies > Windows Settings > Security Settings > Windows Firewall with Advanced Security > Windows Firewall with Advanced Security > Inbound Rules node.
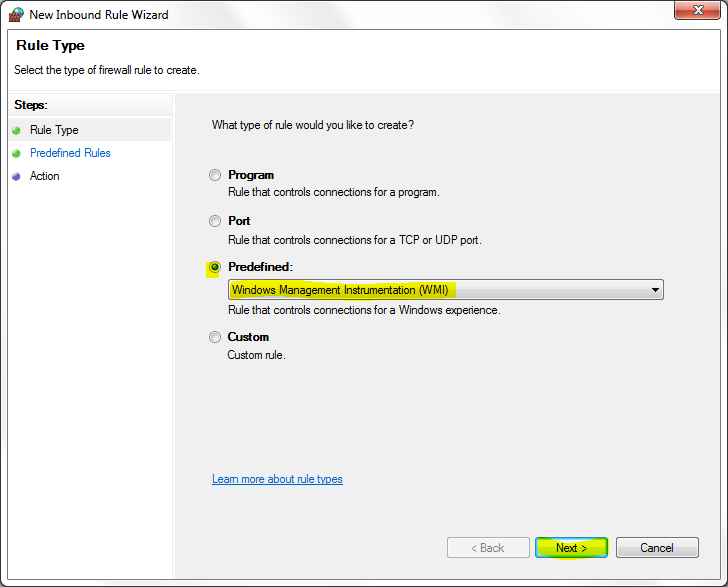
- Check the Predefined radio button and select Windows Management Instrumentation (WMI) from the drop-down list. Click Next.
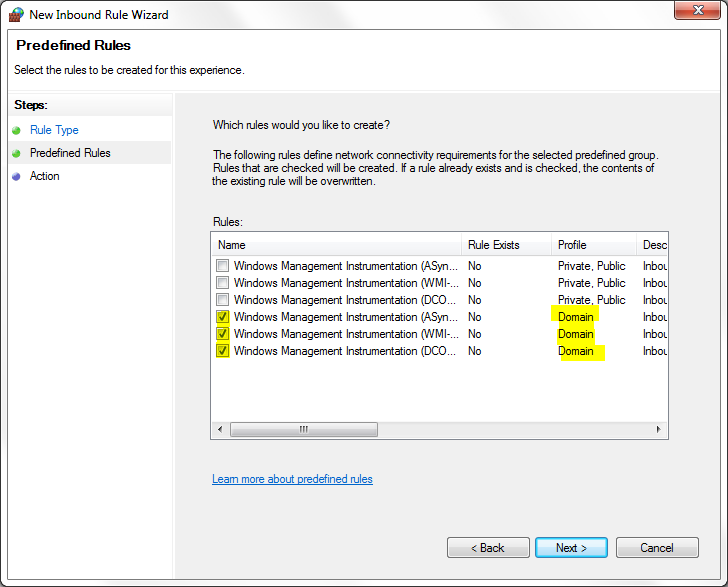
- Check the WMI rules for the Domain Profile, and click Next.
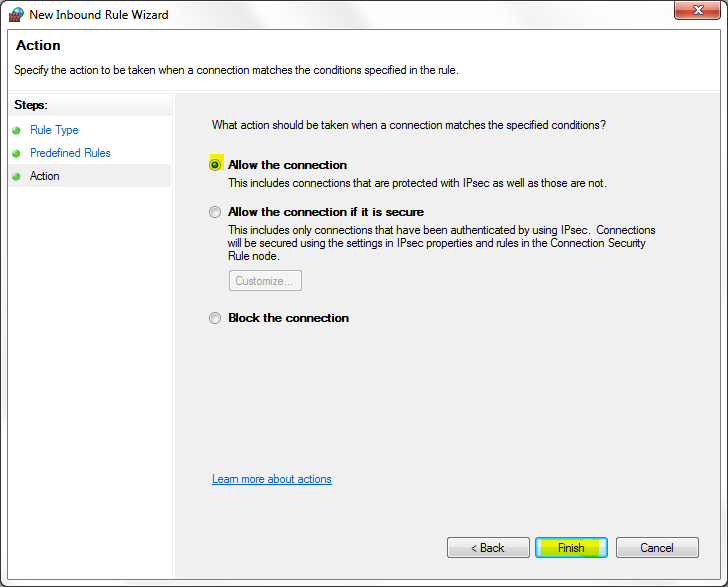
- Check the Allow the Connection radio button and click Finish to exit and save the new rule.
- Make sure the Group Policy Object is applied to the relevant computers using the Group Policy Management Tool.
- Repeat steps 1 through 6 on each instance that must be monitored.
- Ensure the Windows user running the ArcGIS Monitor Service <Name> on the ArcGIS Monitor Administrator machine also has admin permissions or WMI permissions on the target hostname to be monitored.
- Use Windows Perfmon on the ArcGIS Monitor Administrator machine to verify a successful connection to the target hostname in AWS.
- Proceed to Add a System counter
Article ID: 000019267
- ArcGIS Monitor Administrator
- ArcGIS Monitor Server
Get help from ArcGIS experts
Start chatting now

